Active Directory Lightweight Directory Services Windows Server 2008
Windows Server 2008 or later servers:
If you are using Windows Server 2008 or later versions of the servers then this service included in the Server Roles in Server Manager. To install this service then please follow steps below.
1. Open Server Manager.
![[clip_image002[6].jpg]](https://lh5.ggpht.com/_HD--dVed4RY/TYAfS94JPpI/AAAAAAAAADA/mb4TvmPeshA/s1600/clip_image002%5B6%5D.jpg)
3. On the main panel window you see all the roles installed. And on the right side, you have option to add/remove roles.
4. Click on Add Roles link.
5. A wizard opens up and in the window you will see all roles available on the server. If any role installed then it will be disabled as we have clicked on “Add Roles” option.
![[clip_image004[4].jpg]](https://lh4.ggpht.com/_HD--dVed4RY/TYAfUY2mFrI/AAAAAAAAADI/Rxy2UKSnRl0/s1600/clip_image004%5B4%5D.jpg)
6. From the list of roles, select “Active Directory Lightweight Directory Services”.
7. Click “Next” button and then install.
8. It will take around a minute and completes the installation.
Note: It will be good if you restart your server but, not mandatory.
Windows 7:
· Download the installer from “AD-LDS for Windows 7”.
· Run the download and wait till installation complete.
Configuring the AD-LDS
I am assuming you are successfully installed the AD-LDS on the system you are using either WS 2008/R2 or Windows 7. If successfully installed then you will find an option named “Active Directory Lightweight Directory Services Setup Wizard” under control panel -> administrative tools.
![[clip_image005[5].png]](https://lh5.ggpht.com/_HD--dVed4RY/TYAfVrjetmI/AAAAAAAAADQ/XlZqNuBUrPM/s640/clip_image005%5B5%5D.png)
As we discussed earlier, it allows multiple instances in the same server. So, you can create n number of AD-LDS instances on the server. But, when you create an instance what are actually created and what services it enables etc. in later sections. The physical location of this setup wizard is at “%SystemRoot%\ADAM\adaminstall.exe”. OK, now we have to create an instance of the AD-LDS.
· Double click on the “Active Directory Lightweight Directory Services Setup Wizard”.
· It brings up a wizard where we can create a new instance or create a copy of existing instance.
![[clip_image007[4].jpg]](https://lh3.ggpht.com/_HD--dVed4RY/TYAfXhx0pjI/AAAAAAAAADY/33A0tVzc2l4/s400/clip_image007%5B4%5D.jpg)
· Chose option “A unique instance” as we are going to create a new AD-LDS instance and click “Next”.
· Give a good name in the “instance name” and type some description. The name should be good because this name will be used in some other places. So, keep giving good names everywhere.
![[clip_image008[4].png]](https://lh5.ggpht.com/_HD--dVed4RY/TYAfYzj9v0I/AAAAAAAAADg/5v6ZpcKhcqg/s1600/clip_image008%5B4%5D.png)
· Click “Next” and from this screen, we have to choose the port numbers. By default it will take 389 for LDAP and for SSL 636. You can change it.
![[clip_image010[4].jpg]](https://lh4.ggpht.com/_HD--dVed4RY/TYAfayzEbNI/AAAAAAAAADo/r4xzIJjPskw/s1600/clip_image010%5B4%5D.jpg)
· Click “Next” and select the option “Yes, create an application directory partition” and enter the partition name. I have used “CN=Customers,DC=Northwind,DC=Extranet”.
![[clip_image012[5].jpg]](https://lh3.ggpht.com/_HD--dVed4RY/TYAfcsqAPKI/AAAAAAAAADw/cNWv4G9Rl7s/s1600/clip_image012%5B5%5D.jpg)
· Click “Next” and from this screen, we have to give the file locations of where the files will be saved. I left to the default path, but you can give any safe location other than “C:\”
![[clip_image014[4].jpg]](https://lh5.ggpht.com/_HD--dVed4RY/TYAfeWuTGXI/AAAAAAAAAD4/YCSPpNytRgY/s1600/clip_image014%5B4%5D.jpg)
![[clip_image016[4].jpg]](https://lh3.ggpht.com/_HD--dVed4RY/TYAfgsOc61I/AAAAAAAAAEA/fYhvfTD5gfs/s1600/clip_image016%5B4%5D.jpg)
· Click “Next” and select the AD-LDS administrators. If you logged into the server who is an administrator then leave as is, otherwise chose an account.
![[clip_image018[4].jpg]](https://lh3.ggpht.com/_HD--dVed4RY/TYAfiFx2HNI/AAAAAAAAAEI/iQvCjs4L5wk/s400/clip_image018%5B4%5D.jpg)
· Click “Next” and here is the interesting part. What LDIF [Lightweight Directory Interchange Format] files you want to import into this AD-LDS. The physical location of all these LDF files is at “%SystemRoot%\ADAM”. [You can see *.ldf files from Command Prompt]. Select all 4 I selected. It is not mandatory to select all. But, MS-User.LDF is mandatory. All other for adding external properties to user or related classes.
![[clip_image020[4].jpg]](https://lh3.ggpht.com/_HD--dVed4RY/TYAfkDTOqPI/AAAAAAAAAEQ/Nh1BHm18ckE/s400/clip_image020%5B4%5D.jpg)
· Click “Next” and this screen gives the complete summary of what we have selected “Ready to install”.
![[clip_image022[4].jpg]](https://lh3.ggpht.com/_HD--dVed4RY/TYAflws_HBI/AAAAAAAAAEY/uK7qmTl_0Kg/s400/clip_image022%5B4%5D.jpg)
![[clip_image024[4].jpg]](https://lh4.ggpht.com/_HD--dVed4RY/TYAfn0cQtMI/AAAAAAAAAEg/38yfBmhKUUw/s400/clip_image024%5B4%5D.jpg)
· Click Finish. We are completed with installation process.
![[clip_image026[4].jpg]](https://lh4.ggpht.com/_HD--dVed4RY/TYAfpI9f8gI/AAAAAAAAAEo/cC7mCO4uZTI/s400/clip_image026%5B4%5D.jpg)
Validate AD-LDS:
· If everything configured correct then you will see the service running under Administrative Tools -> Services.
![[clip_image028[4].jpg]](https://lh3.ggpht.com/_HD--dVed4RY/TYAfqsAgJxI/AAAAAAAAAEw/ZdFdKhc7eD4/s400/clip_image028%5B4%5D.jpg)
· Go to Control Panel -> Programs and Features -> you will see the AD-LDS instance installed.
![[clip_image030[4].jpg]](https://lh5.ggpht.com/_HD--dVed4RY/TYAfsAHwFmI/AAAAAAAAAE4/StWM_WKuYfI/s640/clip_image030%5B4%5D.jpg)
Connect to the AD-LDS
OK, we successfully created and validated everything is successful. Now, we have to see the created instances and do some stuff with it. For this we need some sort of tool to connect to the instance and browse through. The familiar tool what we use regularly is “ADSI Edit”. Go to Control Panel -> Administrative Tools and open ADSI Edit.
![[clip_image032[4].jpg]](https://lh5.ggpht.com/_HD--dVed4RY/TYAfuK0k1uI/AAAAAAAAAFA/toKPJziNya8/s1600/clip_image032%5B4%5D.jpg)
· Now connect to the AD-LDS instance from the option Actions -> Connect to. Give some name to the connection. And from the Connection point, we will check the schema first. So, select Schema. And from the Computer setting, give your server name. And click OK.
![[clip_image034[4].jpg]](https://lh5.ggpht.com/_HD--dVed4RY/TYAfv6ZdTSI/AAAAAAAAAFI/CGdHlhyA3zc/s400/clip_image034%5B4%5D.jpg)
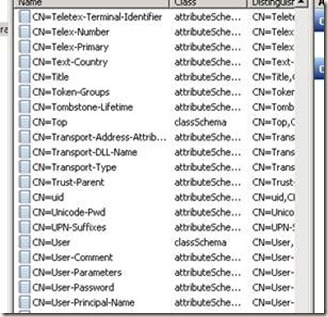
![[clip_image037[4].png]](https://lh3.ggpht.com/_HD--dVed4RY/TYAfzWWxArI/AAAAAAAAAFY/uNETDvUnQAo/s400/clip_image037%5B4%5D.png)
– By default only 4 objects. We have to create an object[Container] named Users to place all the users in it. For that right click on the surface and from the menu, chose new and then object.
![[clip_image039[4].jpg]](https://lh3.ggpht.com/_HD--dVed4RY/TYAf1NYShfI/AAAAAAAAAFg/ik1cn3PnML4/s1600/clip_image039%5B4%5D.jpg)
![[clip_image041[4].jpg]](https://lh3.ggpht.com/_HD--dVed4RY/TYAf2R2B2bI/AAAAAAAAAFo/b62bjAOwJsA/s400/clip_image041%5B4%5D.jpg)
![[clip_image043[4].jpg]](https://lh4.ggpht.com/_HD--dVed4RY/TYAf3c6WBvI/AAAAAAAAAFw/8keZuAjBY9M/s400/clip_image043%5B4%5D.jpg)
– Click Finish. Now you see “Users” container.
– Now, expand the “Users” container from left navigation tree and you will see it is empty.
– Create a user in that “Users” container by right clicking on the surface, from Menu, select New -> Object.
– From the “create new object” window select “User”.
– In next screen, give the name of the user.
– Click Finish. User is created in the “Users” container.
– Before use this user we have to set some properties.
– Right click on user and select “Reset Password”.
![[clip_image044[4].png]](https://lh4.ggpht.com/_HD--dVed4RY/TYAf47pIcVI/AAAAAAAAAF4/3gLqG-azHL8/s1600/clip_image044%5B4%5D.png)
– After than right click on the user and select “Properties”.
– From the list of properties available to the user, set the property “msDS- UserAccountDisabled” to false.
![[clip_image046[4].jpg]](https://lh5.ggpht.com/_HD--dVed4RY/TYAf6UQHxQI/AAAAAAAAAGA/yrcqLv68Bf8/s400/clip_image046%5B4%5D.jpg)
![[clip_image048[4].jpg]](https://lh4.ggpht.com/_HD--dVed4RY/TYAf7wjc8eI/AAAAAAAAAGI/ur7bN2P-u9g/s1600/clip_image048%5B4%5D.jpg)
· From properties, you will find a property named “member”.
![[clip_image050[4].jpg]](https://lh4.ggpht.com/_HD--dVed4RY/TYAf9Iovk2I/AAAAAAAAAGQ/7tSHcn8tVvc/s400/clip_image050%5B4%5D.jpg)
· Click on “Member” and select “Edit”.
· Add users from this window. If user is windows account user then select the option “Add Windows Account” and choose user and save your changes.
OK. We have completed successfully installing, configuring and creating users in the AD-LDS instance. Now, we can use this AD-LDS in our applications to access user information or authentication. It is very to manage, create or replicate the instances in AD-LDS as like ADAM.


How does one learn differing web blogs on Blog writer with keyword or query?